51-3
Cisco ASA 5500 Series Configuration Guide using ASDM
Chapter 51 Information About Cisco Unified Communications Proxy Features
TLS Proxy Applications in Cisco Unified Communications
The ASA provides perimeter security by encrypting signaling connections between enterprises and
preventing unathorized calls. An ASA running the Cisco Intercompany Media Engine Proxy can either
be deployed as an Internet firewall or be designated as a Cisco Intercompany Media Engine Proxy and
placed in the DMZ, off the path of the regular Internet traffic.
TLS Proxy Applications in Cisco Unified Communications
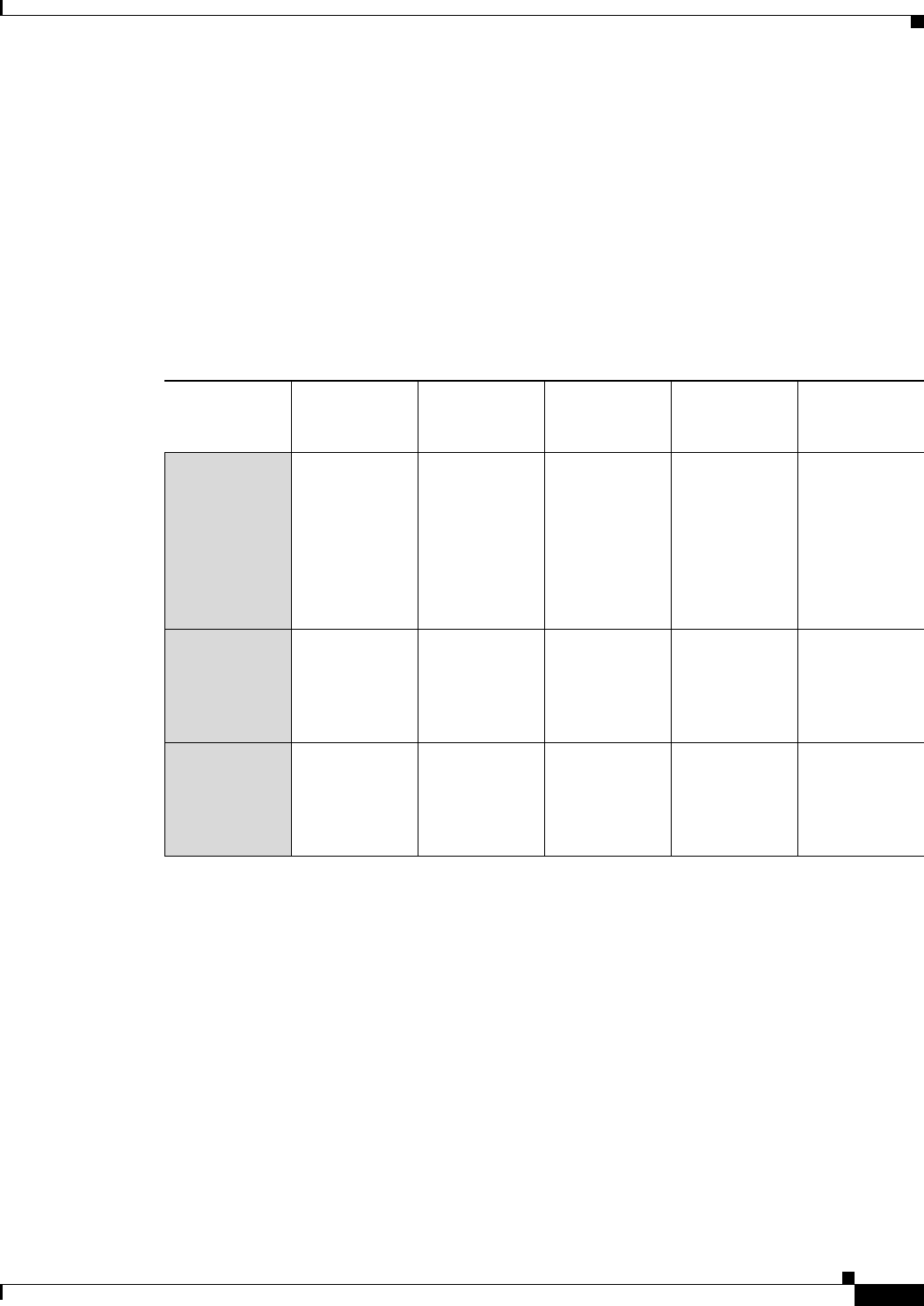
Table 51-1 shows the Cisco Unified Communications applications that utilize the TLS proxy on the
ASA.
The ASA supports TLS proxy for various voice applications. For the phone proxy, the TLS proxy
running on the ASA has the following key features:
• The ASA forces remote IP phones connecting to the phone proxy through the Internet to be in
secured mode even when the Cisco UCM cluster is in non-secure mode.
• The TLS proxy is implemented on the ASA to intercept the TLS signaling from IP phones.
• The TLS proxy decrypts the packets, sends packets to the inspection engine for NAT rewrite and
protocol conformance, optionally encrypts packets, and sends them to Cisco UCM or sends them in
clear text if the IP phone is configured to be in nonsecure mode on the Cisco UCM.
• The ASA acts as a media terminator as needed and translates between SRTP and RTP media streams.
• The TLS proxy is a transparent proxy that works based on establishing trusted relationship between
the TLS client, the proxy (the ASA), and the TLS server.
Table 51-1 TLS Proxy Applications and the Security Appliance
Application TLS Client TLS Server
Client
Authentication
Security
Appliance
Server Role
Security
Appliance
Client Role
Phone Proxy
and TLS Proxy
IP phone Cisco UCM Yes Proxy
certificate,
self-signed or
by internal CA
Local dynamic
certificate
signed by the
ASA CA
(might not need
certificate for
phone proxy
application)
Mobility Proxy Cisco UMC Cisco UMA No Using the
Cisco UMA
private key or
certificate
impersonation
Any static
configured
certificate
Presence
Federation
Proxy
Cisco UP or
MS LCS/OCS
Cisco UP or
MS LCS/OCS
Yes Proxy
certificate,
self-signed or
by internal CA
Using the
Cisco UP
private key or
certificate
impersonation


















