B-14
Cisco ASA 5500 Series Configuration Guide using ASDM
Appendix B Configuring an External Server for Authorization and Authentication
Configuring an External LDAP Server
Cisco AV Pairs ACL Examples
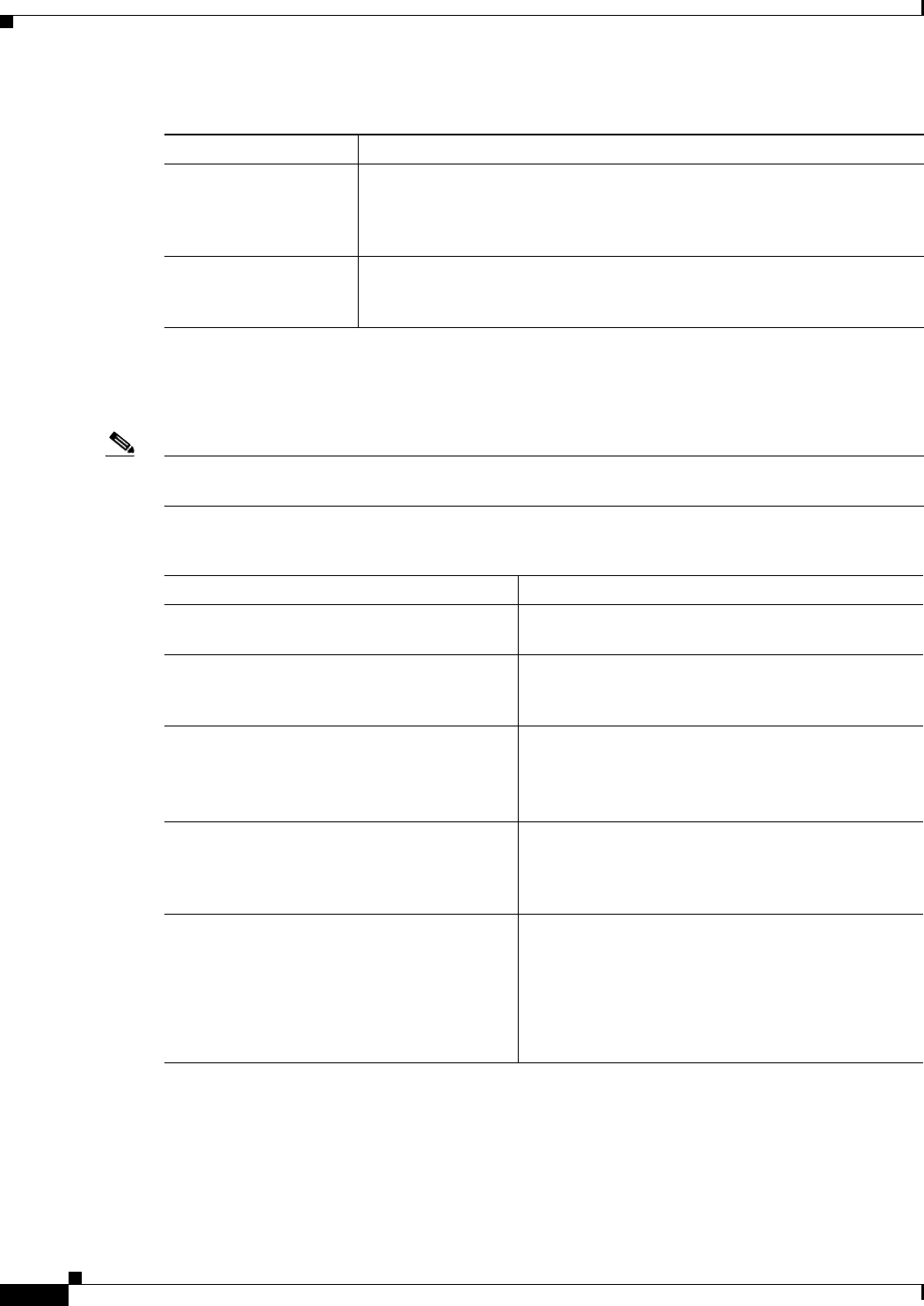
Table B-4 shows examples of Cisco AV pairs and describes the permit or deny actions that result.
Note Each ACL # in inacl# must be unique. However, they do not need to be sequential (for example, 1, 2, 3,
4). That is, they could be 5, 45, 135.
URL Types Supported in ACLs
The URL may be a partial URL, contain wildcards for the server, or include a port.
Source Network or host that sends the packet. Specify it as an IP address, a
hostname, or the any keyword. If using an IP address, the source wildcard
mask must follow. This field does not apply to Clientless SSL VPN because
the ASA has the role of the source or proxy.
Source Wildcard Mask The wildcard mask that applies to the source address. This field does not
apply to Clientless SSL VPN because the ASA has the role of the source or
proxy.
Table B-3 AV-Pair Attribute Syntax Rules (continued)
Field Description
Table B-4 Examples of Cisco AV Pairs and Their Permitting or Denying Action
Cisco AV Pair Example Permitting or Denying Action
ip:inacl#1=deny ip 10.155.10.0 0.0.0.255
10.159.2.0 0.0.0.255 log
Allows IP traffic between the two hosts using a full
tunnel IPsec or SSL VPN client.
ip:inacl#2=permit TCP any host
10.160.0.1 eq 80 log
Allows TCP traffic from all hosts to the specific host
on port 80 only using a full tunnel IPsec or SSL VPN
client.
webvpn:inacl#1=permit url
http://www.example.com
webvpn:inacl#2=deny url smtp://server
webvpn:inacl#3=permit url
cifs://server/share
Allows clientlessSSL VPN traffic to the URL
specified, denies SMTP traffic to a specific server,
and allows file share access (CIFS) to the specified
server.
webvpn:inacl#1=permit tcp 10.86.1.2 eq
2222 log
webvpn:inacl#2=deny tcp 10.86.1.2 eq
2323 log
Denies Telnet access and permits SSH access on
non-default ports 2323 and 2222, respectively, or
other application traffic flows using these ports for
clientless SSL VPN.
webvpn:inacl#1=permit url
ssh://10.86.1.2
webvpn:inacl#35=permit tcp 10.86.1.5 eq
22 log
webvpn:inacl#48=deny url
telnet://10.86.1.2
webvpn:inacl#100=deny tcp 10.86.1.6 eq
23
Allows clientless SSL VPN SSH access to default
port 22 and denies Telnet access to port 23,
respectively. This example assumes that you are using
Telnet or SSH Java plug-ins enforced by these ACLs.


















