Brocade Network Advisor IP User Manual 629
53-1003056-01
Security configuration deployment
18
Security configuration deployment
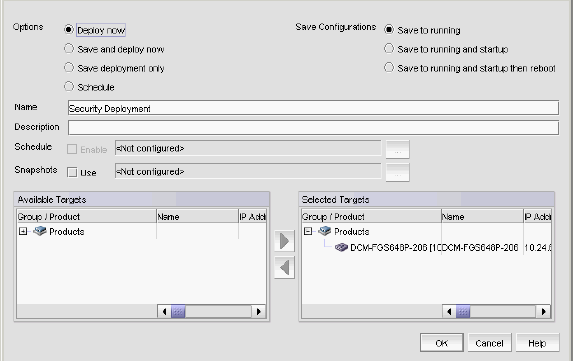
Figure 235 shows the standard interface used to deploy security configurations.
FIGURE 235 Deploy to Product/Ports dialog box
Before you can deploy a security configuration, you must create the security configuration. For
step-by-step instructions, refer to the following sections:
• “Layer 2 access control list management” on page 561
• “Layer 3 access control list policy” on page 580
• “Media Access Control (MAC) filter management” on page 620
Security Management enables you to configure, persist, and manage a security configuration as a
“deployment configuration object”. A deployment configuration object is comprised of the following
parts:
• Security configuration (Layer 2 ACL, L3 ACL, or MAC filter)
• Target information
• Deployment option
• Persistence option
• Scheduling option
• Snapshot option
To create a deployment configuration object, you must save the deployment. Once you create a
deployment configuration object, you can access the security configuration from the Deployment
manager. For more information about the Deployment manager, refer to “Deployment Manager” on
page 963.


















