564 CHAPTER 40: CONFIGURING IPSEC
authentication and encryption, for instance), it is necessary to create two different
encryption access control lists and apply them to different security policies.
Encryption access control list can be used to judge both inbound communication
and outbound communication.
To create an encryption access control list, perform the following configurations in
system view.
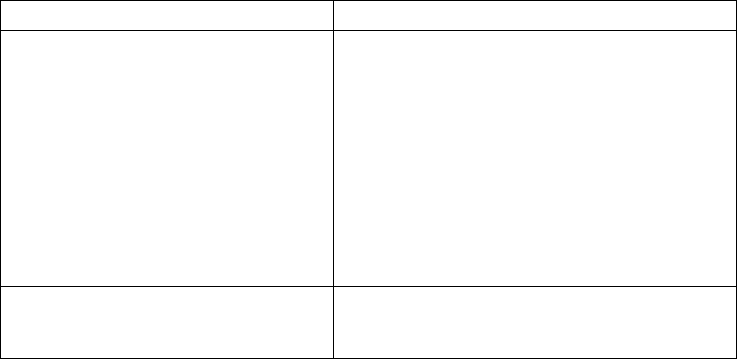
Table 630 Create Encryption Access Control List
The information transmitted between the source and destination addresses
specified by the
permit key word is encrypted/decrypted by the peer router.
The deny key word does not allow the defined policy to be applied in the security
policy. This can prevent the router from encrypting or decrypting communication
information. (that is to say not allowing the policy defined in this security policy to
be applied). If all the security policies on an interface are denied, this
communication is not protected by encryption.
Do not use the wildcard any in the source address and destination address of the
command
rule when creating an encryption ACL. This is because when the data
packet enters the router, and is sent to a router not configured with encryption,
the key word
any will cause the router to try to establish encryption session with a
router without encryption.
The encryption access list defined at local router must have a mirror encryption
access list defined by the remote router so that the communication contents
encrypted locally can be decrypted remotely.
When the user uses the display acl command to browse the access lists of the
router, all extended IP access lists, including those for both communication
filtering and for encryption, will be displayed in the command outputs. That is to
say, these two kinds of extended access lists for different purposes are not
distinguished in the screen output information.
Operation Command
Establish encryption access control list
(applicable to IPSec software and crypto
card)
acl acl-number [ match-order config |
auto ]
rule { normal | special }{ permit |
deny } pro-number [source
source-addr source-wildcard | any ]
[source-port operator port1 [ port2 ]
] [ destination dest-addr dest-
wildcard | any ] [destination-port
operator port1 [ port2 ] ]
[icmp-type icmp-type icmp-code]
[logging]
Delete encryption access control list
(applicable to IPSec software and crypto
card)
undo rule { rule-id | normal |
special }
undo acl {acl-number| all }


















