Creating a Security Policy 569
higher priority. When a security policy group is applied on an interface, actually
multiple different security policies in this security policy group are applied on it
at the same time, so that different data streams are protected by different SAs.
Creating a Security
Policy Manually
Perform the following configurations in system view.
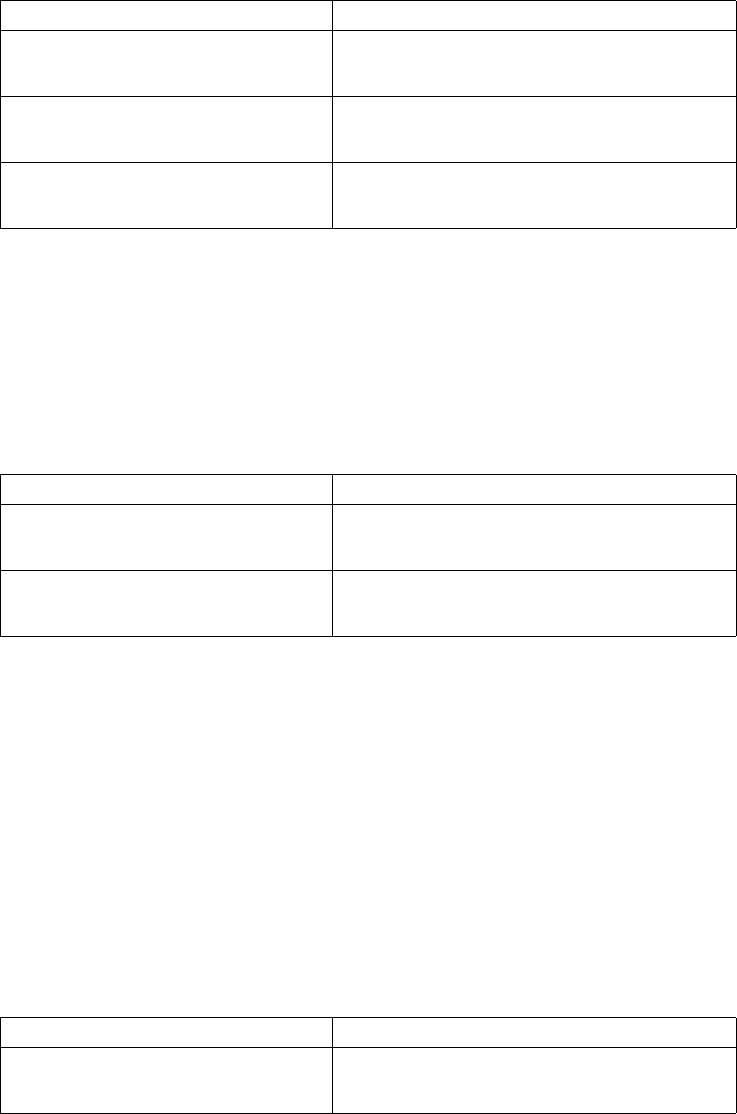
Table 639 Establish Security Policy Manually
By default, no security policy is created.
Configure access control list quoted in security policy
After a security policy is created, it is also necessary to specify the quoted
encryption access control list item for it to judge which inbound/outbound
communications should be encrypted and which should not.
Perform the following configurations in IPSec policy view.
Table 640 Configure Encryption Access Control List Quoted in Security Policy
By default, no encryption access control list is quoted in the security policy.
Set start point and end point of security tunnel
The channel with security policy applied is usually called a security tunnel. A
security tunnel is established between local and peer gateways, so the local
address and the remote address must be set correctly to successfully establish a
security tunnel.
For the security policy created manually, only one remote address can be specified.
To set a new remote address, the previously specified one must be deleted first.
Only when both local address and remote address are set correctly can a security
tunnel be created.
Perform the following configurations in IPSec policy view.
Table 641 Specify Start Point and End Point of Security Tunnel
Operation Command
Create security policy manually to enter
IPSec policy view(applicable to IPSec
software and crypto card)
ipsec policy policy-name
sequence-number manual
Modify the created security policy
manually (applicable to IPSec software and
crypto card)
ipsec policy policy-name
sequence-number
Delete the created security policy
(applicable to IPSec software and crypto
card)
undo ipsec policy policy-name
sequence-number
Operation Command
Configure encryption access control list
quoted in security policy (applicable to
IPSec software and crypto card)
security acl access-list-number
Cancel encryption access control list
quoted in security policy (applicable to
IPSec software and crypto card)
undo security acl
Operation Command
Set local address of security tunnel
(applicable to IPSec software and crypto
card)
tunnel local ip-address


















