2-16
Cisco ASDM User Guide
OL-16647-01
Chapter 2 Introduction to the Security Appliance
Firewall Functional Overview
Firewall Functional Overview
Firewalls protect inside networks from unauthorized access by users on an outside network. A firewall
can also protect inside networks from each other, for example, by keeping a human resources network
separate from a user network. If you have network resources that need to be available to an outside user,
such as a web or FTP server, you can place these resources on a separate network behind the firewall,
called a demilitarized zone (DMZ). The firewall allows limited access to the DMZ, but because the DMZ
only includes the public servers, an attack there only affects the servers and does not affect the other
inside networks. You can also control when inside users access outside networks (for example, access to
the Internet), by allowing only certain addresses out, by requiring authentication or authorization, or by
coordinating with an external URL filtering server.
When discussing networks connected to a firewall, the outside network is in front of the firewall, the
inside network is protected and behind the firewall, and a DMZ, while behind the firewall, allows limited
access to outside users. Because the security appliance lets you configure many interfaces with varied
security policies, including many inside interfaces, many DMZs, and even many outside interfaces if
desired, these terms are used in a general sense only.
This section includes the following topics:
• Security Policy Overview, page 2-16
• Firewall Mode Overview, page 2-19
• Stateful Inspection Overview, page 2-19
Security Policy Overview
A security policy determines which traffic is allowed to pass through the firewall to access another
network. By default, the security appliance allows traffic to flow freely from an inside network (higher
security level) to an outside network (lower security level). You can apply actions to traffic to customize
the security policy. This section includes the following topics:
• Permitting or Denying Traffic with Access Lists, page 2-17
• Applying NAT, page 2-17
• Protecting from IP Fragments, page 2-17
• Using AAA for Through Traffic, page 2-17
• Applying HTTP, HTTPS, or FTP Filtering, page 2-17
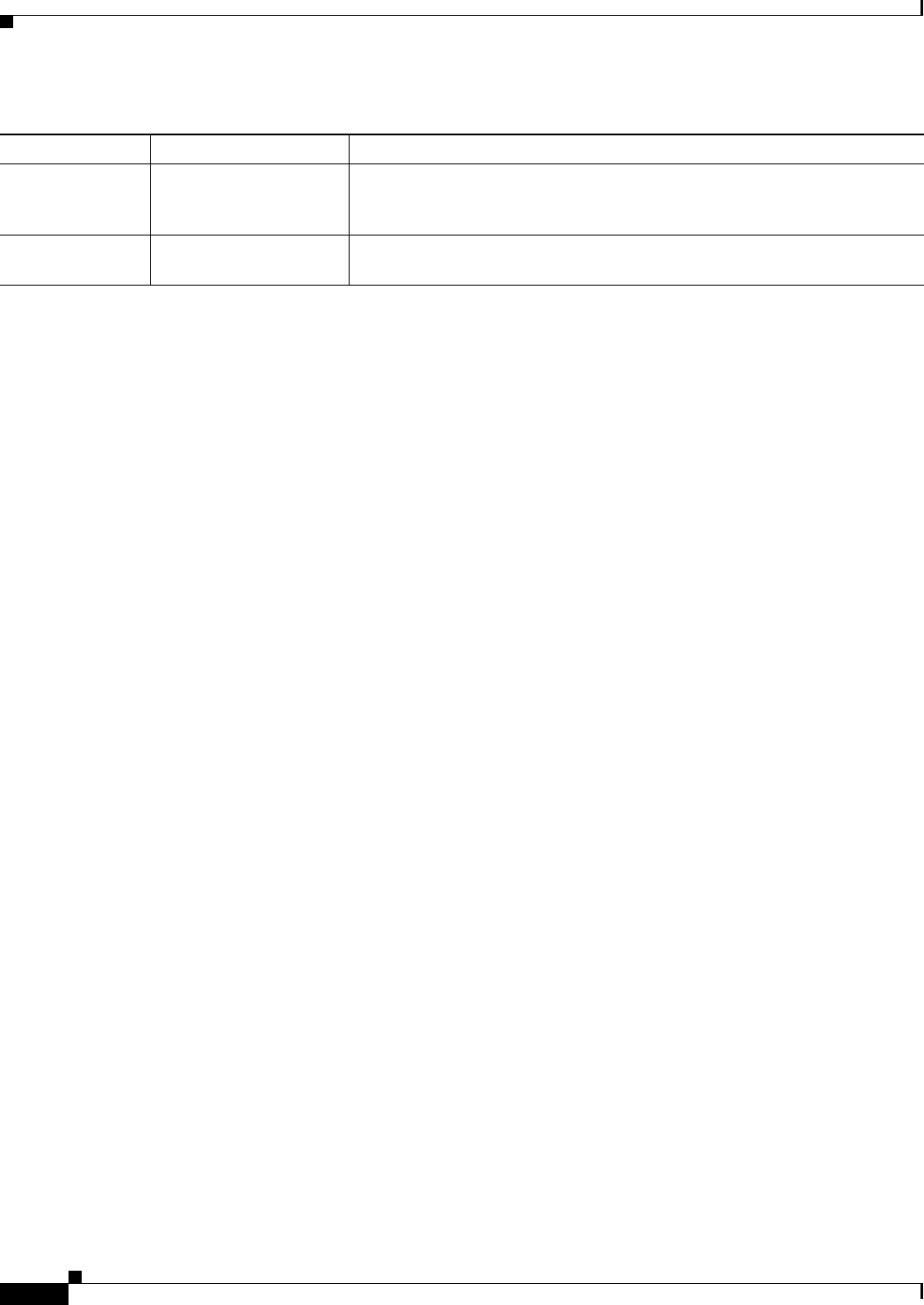
Logging Secure logging You can enable secure connections to the syslog server using SSL or TLS
with TCP, and encrypted system log message content. Not supported on the
PIX series adaptive security appliance.
IPv6 IPv6 support for SIP The SIP inspection engine supports IPv6 addresses. IPv6 addresses can be
used in URLs, in the Via header field, and SDP fields.
1. Clientless SSL VPN features are not supported on the PIX security appliance.
2. TLS proxy is not supported on the PIX security appliance.
Table 2-5 New Features for ASA and PIX Version 8.0(2) (continued)
ASA Feature Type Feature Description


















